OUR EXPERTISE
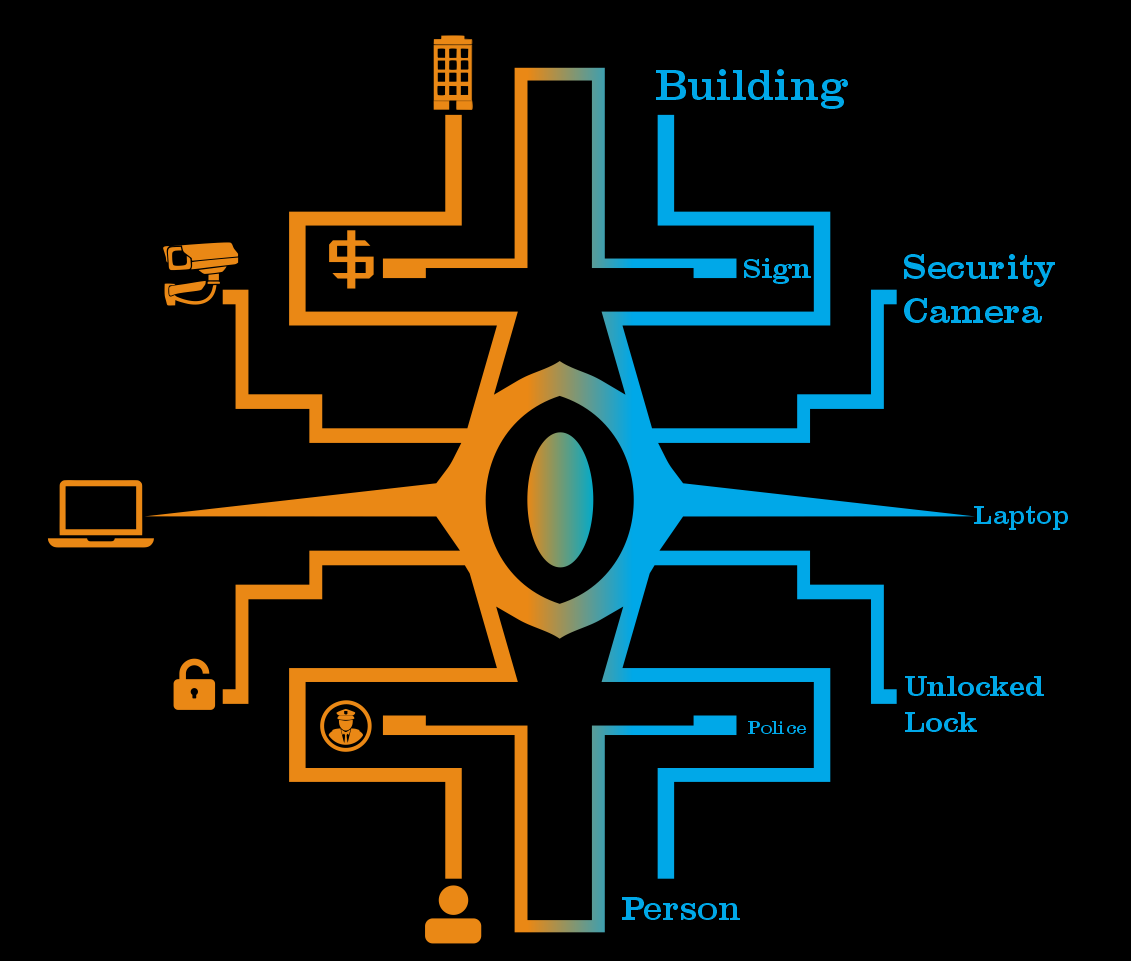
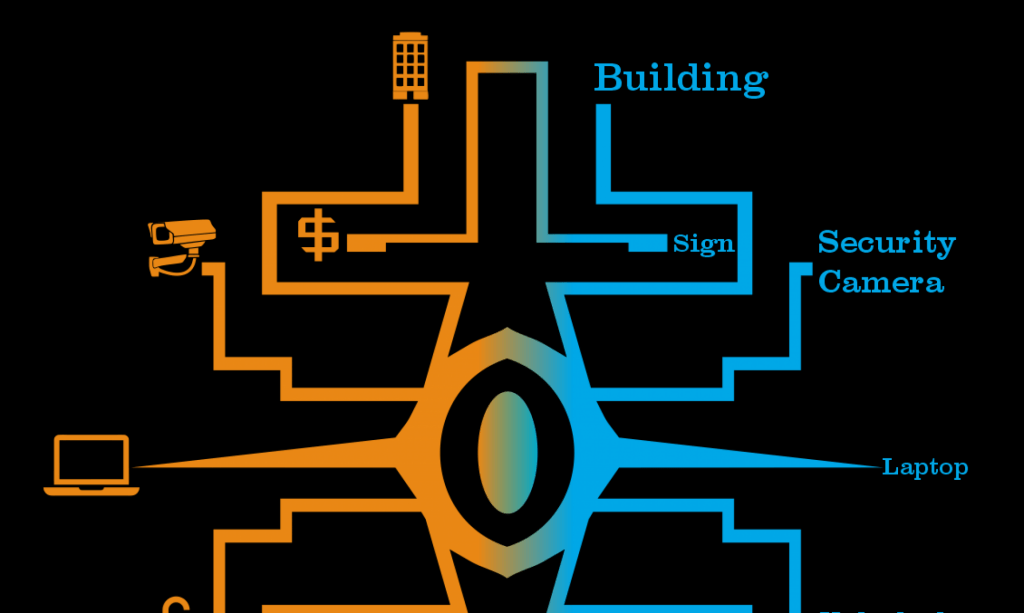
Converged Security
Converged Security is the operational concept of understanding, operating, measuring, and maturing all areas of security of an organization. Including but not limited to Physical Security, Cyber Security, Investigations, Executive Protection, Law Enforcement Support, Information Security, Fraud, etc. We are able to solve stressors, issues, problems, and challenges in these areas and more, in a Small Medium Business (SMB), Non-Government Organization (NGO), Faith Based Organization, Enterprise, Carrier, Government and Classified environments. If we don’t feel 100% comfortable we can provide you amazing service we will professionally guide you to another resource, we trust, that can better serve you.

Jim McConnell
CEO/CSO/Principal
Ask McConnell, LLC – Your Converged Security Services Provider
WHAT WE DO
Security Pain Points, Stressors, Ideas We Solve

Don’t like your answers to the questions when you ask the person in the mirror about:

Insider Threat

Mergers & Acquisitions / Divestiture

Seat at the Table

Supply Chain Security

Physical Security Vulnerability Discovery

Training Program Management

Executive Protection Program Management
Security Metrics

Offshore Risk

Security Operations Centers

Crisis Response
Our Solutions
Most consulting first want to assess, advise, help you build, or even fully manage the solution. That’s okay, we think our focus on the follow three ways are where we can bring tremendous value and ROI to your investment in our services. We will glad to help you build or augment your team in the field where we mutually feel that is the best solution.
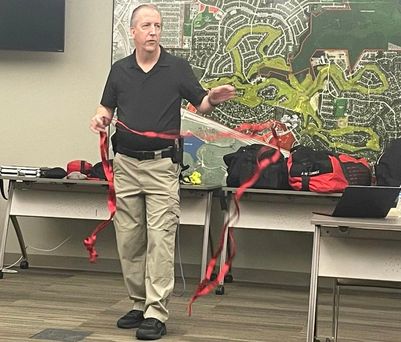
The Teaching Consultant
Jim not only has the privilege of being an Adjunct instructor with Texas A&M – TEEX, but we has taught classes around the world. In addition to the classes we have ready, we are always developing new topics and have access to a set of instructors around the world on all things security. Imagine a “Teaching Menu” that you can select from for your team with extended times for Q&A and “Whiteboarding” and “Brainstorming”.

The Exercising Consultant
(PSA: Please don’t tell my doctor, I actual don’t exercise alot)
Whether a functional tabletop exercise, organizational tabletop exercise, field exercise, cross-dependency exercise, or full scale exercise, we are ready to design, facilitate and/or evaluate the scope of you need exercised, at scale. We can also provide actor and “poker” capabilities to existing exercises
The Measuring Consultant
Whether you are just getting started in metrics/analytics 101, or only focusing on stats vs. metrics. We work with you on the baseline, through SIPOC, of your program then help you setup recurring metrics output options.

The Maturing Consultant
Call it maturity, call it transformation, “take it to the next level”, through metrics and building strategic plans, let’s mature a specific function or overall security program.
Converged Security Academy
A Online Course Academy offering courses for new security professionals, transitions law enforcement and military, high school, college age students and tenured in unique topics

Operations / Staff Augmentation
We are ready to provide one-time, quick response, retainer, staff/team augmentation or fractional services in both a domestic & international regions.
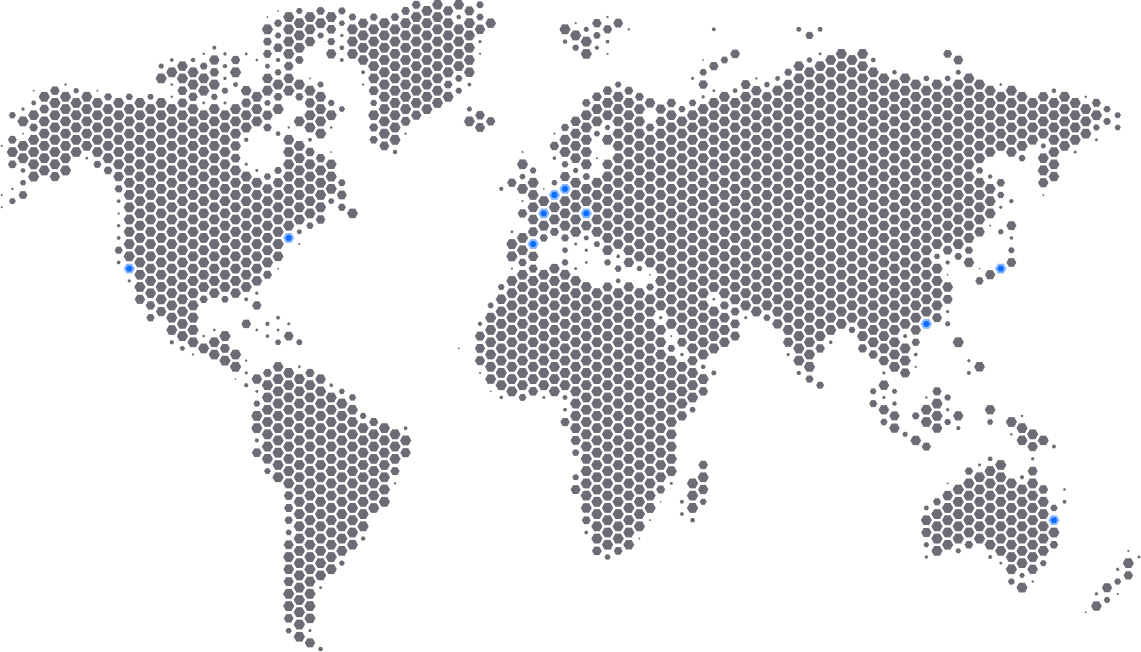
WHERE WE HAVE OPERATED
Past In Country Operations
USA
United Kingdom
Mexico
Costa Rica
Venezuela
Puerto Rico
Argentina
Canada
Thailand
Italy
Dominican Republic
India
New Zealand
Our Core Definitions
We have collected over 100 crazy marketing claims from security and audit firms, so we committed to be transparent for you about how we will use these terms as consistently as we humanly can. These are OUR (and many others in the security world) perspective, you, your organization, your organizational culture may define / scope these words differently.
Security
The prevention, detection, and response to a crime or a violation of an organization’s rules/policies.
Safety
The prevention, detection, and response to an accident. (think spilled milk, broken glass, etc.)
Safe
The FEELING by an individual, in an environment, where they feel the security and safety controls are adequate for them to be at peace to enter/enjoy/use the environment.
All
“All in every language means All” – Pastor Robert Morris. So always remember that your organization’s use of the word “All” needs to mean, every element under an organization’s ownership, control or that impacts an organization’s ability to carry out its mission in a safe manner.

Chief Executive Officer / Chief Security Officer / Principal
CORPORATE SECURITY MANAGEMENT – CONVERGED SECURITY SERVICES, INVESTIGATIONS, MERGERS & ACQUISITION SECURITY, INSIDER THREAT, SUPPLY CHAIN, FRAUD, SUPPLY CHAIN EXPLOITATION, EXECUTIVE/PERSONAL PROTECTION, NATIONAL SECURITY / LAW ENFORCEMENT LIAISON
Jim McConnell is beyond blessed to currently be CEO, CSO and Principal for Ask McConnell, a unique converged security services operations, consultancy, and advisor team. He has over 28 years of Corporate Security operational experience including his most recent role as the first Fellow in Verizon’s Corporate Security Office with his last primary responsibility being program management for and protector on the EP/Special Events Security Team along with other critical activities including Supply Chain Security, Physical Security Kinetic Testing, and Government Liaison support. Jim has operated in country in 12 different countries and has 15 patents under his engineering “hat”. He mentors transitioning military/LEO and has done pro bono security support to over 350 churches for over 30 years and a local volunteer first responder. Jim is also the author new book called Converged Security Metrics.
Certified Fraud Examiner (CFE), Professional Certified Investigator (PCI), Certified Information Systems Security Professional (CISSP), Certified Information Systems Auditor (CISA), Certified Information Systems Manager (CISM), CDPSE, Certified Protection Officer (CPO)*, CPOI*, Security+, ARES Level 3, SARTECH 3, FAA Commercial Part 107 Drone Pilot (sUAS), Ground Search and Rescue (GSAR/WSAR/SAR/USAR) Technician and Team Leader, FEMA USAR/WAS Technician, Wilderness First Aid (WFA), NWCG Wildland Firefighter (FFT2), ARC First Aid/AED/CPR (“Certified” and Instructor), Stop The Bleed (“Certified” and Instructor), licensed in Texas as a Level IV Personal Protection Officer (PPO), Texas Private Security Licensed Business, Texas Private Investigator (PI), Texas School Safety Center Consultant, ICA CPTED Professional*, Texas Licensed Real Estate Agent
* In process of renewal/finalizing

Our goal is the first engagement each month is a pro bono faith based organization in need of security support. We also mentor law enforcement and military in transition to Corporate/Private Security along with being a volunteer first responder and supporting the law enforcement family.
Texas PSB Individual License: Active, Texas PSB Business License: C28455301, CAGE Code: 9LXZ3, TCOLE Registered, US Clearance Eligible, EIN: 93-1914843, DUNS: 119058091
